Key loss prevention

High security solutions for protecting valuable keys and other shared portable equipment.
Whether you want to prevent keys from leaving the building, alert staff to their responsibilities if they do leave the building with them or simply know whereabouts they are; with our key loss prevention solutions you can do it all.
The way in which you manage your businesses keys can dramatically impact the security of the assets they access. Whilst electronic key cabinets can help reduce issues by making people accountable for the keys, in critical environments additional protection may be required. Our key loss prevention solutions combine deister’s RFID technologies to provide you with more than just a method to monitor and control keys.
Key control
Manage who can access each set of keys without the need for a physical presence.
Ensuring personnel can only access keys they are authorised to use is important to prevent compromise, although managing this can be difficult and expensive. With our key control solution, the entire process can be automated!
Your personnel identify themselves at the cabinet using an access card, fob, PIN or biometrics. This will only allow them to open the cabinet and remove keys if you have given them permission. You can control each key or users individual access rights from any location using our web-based platform. With no need for staff to physically monitor and control the issuing and returns process, your staffs time can be used more efficiently whilst reducing your key-related costs.
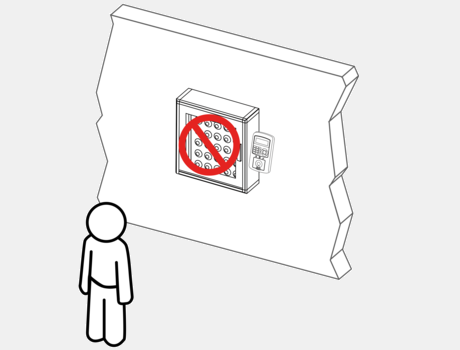
Exit prevention
Prevent your organisations keys from being taken from the building.
In high security environments, the risk of compromise is too great to allow keys to leave the premise. With our exit prevention solutions, stopping someone from exiting the building if they have a key is simple.
When a user takes a key, this can automatically block their ability to exit the building until it is returned. If you require further protection, then we can prevent doors from opening when a key is within range. This ensures that your important keys remain within your facility.
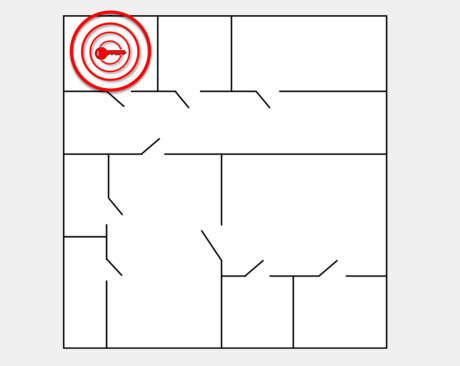
Unauthorised zone alert
Safeguard your keys from disappearing from their designated zones.
Making sure your keys remain within their building area can be a challenge. But with our solution, you can track the use of keys as well as warn users when they are being taken out of their designated areas.
Our unauthorised zone alert solution triggers an alarm when a key is taken into a zone it should not be in. By alerting your staff, they are made aware of the company assets they are in possession of and reminded that they should not be taking it within that zone. This can be beneficial if you have secure areas or controlled environments where certain keys could be at risk or compromise the area.
Additional information
Introduction to key management
Find out how electronic key management systems can help your organisation.
How keys could be costing your business
Learn how keys could be negatively impacting your businesses.